Protecting confidential documents

Protection of commercially sensitive and confidential documents.
Protecting confidential and commercially sensitive documents requires more than just encryption. Here we explain why document DRM is required to control how documents are used once they have been distributed.
 Protect confidential & sensitive documents – stop sharing and leakage
Protect confidential & sensitive documents – stop sharing and leakage
There is a broad range of documents in the organization that contain confidential, commercially sensitive, or personally sensitive information. Some of them are just for internal use. Others must be shared with a bewildering array of outside organizations who do not necessarily share your definitions of sensitivity and protection, causing you to enforce your views over theirs.
Locklizard Digital Rights Management (DRM) technologies offer a way forward, allowing the information owner/distributor to exert control over the use of confidential and sensitive documents once they are electronically secured and distributed, preventing recipients from readily misusing or ignoring the constraints the owner wants to apply. This guide will cover:
- Distributing and managing commercially sensitive & confidential documents
- Using DRM to protect confidential & sensitive documents
- What features make DRM controls so good for protecting confidential & sensitive information?
- Why Locklizard to protect your confidential and business-sensitive documents?
 Distributing and managing commercially sensitive & confidential documents
Distributing and managing commercially sensitive & confidential documents

In every organization, there are vast numbers of documents containing sensitive information that should not be in public circulation, including:
- Mergers and acquisitions proposals and documentation
- Internal procedures (including lending criteria and corporate evaluation)
- Legal disclosure (aka Discovery)
- Product planning (including risk analysis)
- Internal inquiries (also investigations)
- Market analyses (own and competitive)
- Business agreements (distribution and licensing)
- Staff reports (disciplinary and review)
- Sales documentation (pricing margins)
- Repair manuals (diagrams, parts lists, substitutions)
- Contracts (tendering process, final terms)
- Board minutes (agenda, surrounding documents, decisions)
- and so on…….
While this appears to be a considerable list, it’s just the tip of the iceberg. There are many types of sensitive information that are specific to certain industries or even certain companies. Regardless, many are still sent on paper, as emails, or as PDF documents with little thought about the confidentiality of the information in them.
 Confidential document solutions and their drawbacks
Confidential document solutions and their drawbacks
How can you protect sensitive data in documents from both authorized and unauthorized users? This is a question enterprises have been trying to find the answer to for several decades. In that time, various confidential document solutions have surfaced, each with unique strengths and challenges.
 PGP encryption
PGP encryption
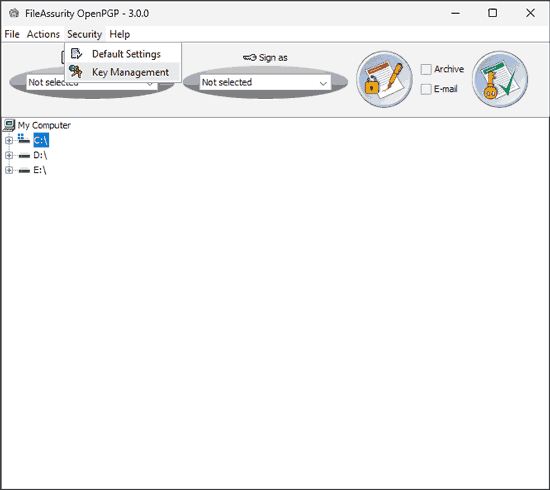
PGP encryption uses public and private key pairs to encrypt files in such a way that only the intended recipient (or someone else with their private key) can decrypt them. PGP is a suitable solution for protecting documents in transit and at rest, provided it uses a strong encryption algorithm.
However, PGP was never designed to protect documents after a user has opened them. It does not look to remove decrypted files after they have been viewed or prevent users from sharing, modifying, or misusing them. Users can still intentionally or unintentionally leak sensitive information, as decrypted PGP documents act exactly the same as the original, unprotected file.
It is additionally worth noting that PGP requires public keys to be exchanged in advance. This can work in some setups, but can quickly become a problem at scale or if you need to share information with outside parties.
 DLP solutions
DLP solutions
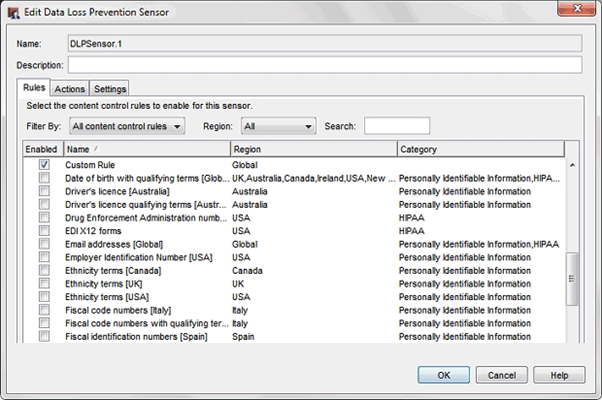
Data Loss prevention solutions take the stance that you can stop sensitive data from leaving the enterprise by watching every exit. Of course, while this might work well for guarding physical locations, it’s much more complex digitally. Sensitive data can leave the enterprise through email, USB, cloud storage, messaging services, mobile devices, social media, and more. Additionally, data may not be left in its original form. Users can change file extensions, use ciphers, encrypt it, compress it with password protection, embed the data in images, split a file into smaller parts, or add it to a document as screenshots.
All of this makes accurate detection very difficult. DLP usually works by defining and categorizing sensitive data and then using a combination of keyword analysis, regular expressions, fingerprinting, and metadata analysis. While emerging AI tools can make DLP solutions more accurate, they can also make it easier to dodge the prevention in sophisticated ways. Ultimately, though DLP solutions can prevent accidental leaks, they can’t prevent intentional leaks with 100% accuracy. In fact, 42% of IT leaders believe that their static DLP tools don’t even stop half of all incidents.
 Cloud document solutions
Cloud document solutions
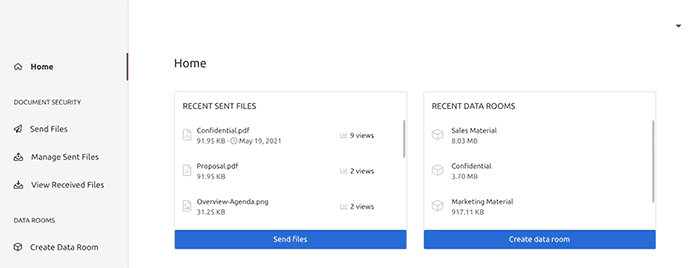
Cloud document solutions were created with a convenience-first mindset – the ability to access documents anywhere and have changes reflected live. However, businesses quickly began to realize that having swathes of sensitive information easily shareable and accessible might not be the best idea. As a result, providers began to adapt, implementing additional security mechanisms such as 2FA, editing/printing restrictions, and letting admins disable link sharing. Some went further by creating private document solutions from the ground up, offering features like end-to-end encryption or adding more complex permissions systems and marketing themselves as “secure deal rooms”.
If only it were so simple. The problem with all web-based solutions is that browsers are inherently and intentionally limited in their control over users’ operating systems. For the most part, a web application can only control what happens inside the browser, and for good reason – it would make it trivial for attackers to compromise your device. As a result, the options for controlling what users can do with documents are limited to JavaScript controls that disable certain functions on the webpage. Users can usually bypass JavaScript controls to download an unprotected copy. The JavaScript must run partially on the user’s machine and can therefore be tampered with using scripts or extensions. Additionally, JavaScript can’t stop things like screenshots, which aren’t handled by the browser at all.
Of course, the other issue with cloud services is that account access is (almost always) governed by a username and password, with 2FA authentication sometimes tacked on. Users can share their login details with others alongside any 2FA codes. While a few services allow you to allow logins only from specific IP addresses, this has its own issues. It doesn’t work well for companies with remote workforces, while having the obvious flaw that IP addresses can be faked using a VPN.
 PDF password protection
PDF password protection
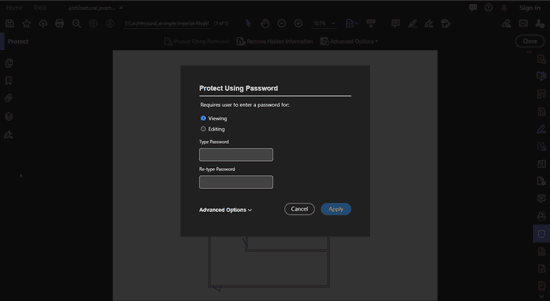
Adobe Acrobat password protection is even less effective than PGP encryption at preventing the leak of sensitive documents. Tying a strong encryption key to a human-set, often non-random password makes it easier for users to remember, but also easier to guess or share. Tools such as Elcomsoft can crack some PDF open passwords in seconds and many others in minutes or hours. And while you might point to Acrobat’s printing and editing controls, they are even easier to bypass. Users can upload the PDF to any number of PDF password removal websites to instantly and trivially strip the permissions password.
 The problem with most confidential document solutions
The problem with most confidential document solutions
The most popular confidential document solutions aren’t effective. In particular, often there is little attention paid to controlling what the recipient can do with the sensitive information after they receive it. This fundamental issue exists with most protection systems. They focus on protecting the information when it is going from one place to another, or while on the server(s). They don’t try to restrict how the recipient can use the information. With sensitive information, you rarely want the recipient to be able to do anything other than view the content, and very rarely to be able to make a printed copy.
This is the central challenge that WikiLeaks, Assange, and Snowden have so ably demonstrated to governments and corporate bodies. Even the most secret national, commercial, and personal information can be trivially copied and redistributed, with the normal security mechanisms seemingly powerless to stop it.
An obvious solution to controlling commercially sensitive and confidential information – implementing DRM document management controls – is only taking shape now. What was the delay?
 Using DRM to protect confidential & sensitive documents – stop sharing and leakage
Using DRM to protect confidential & sensitive documents – stop sharing and leakage

DRM is not a technology that has always been there; otherwise, implementing it would have been a no-brainer. So why has it taken so long to establish high-quality document DRM services?
Historically, attention has always been given to protecting access to files rather than controlling the use of the contents. But the advent of digital publishing has ushered in the requirement for Digital Rights Management (DRM) technologies to be developed that are relevant to documents and their contents.
The concept of DRM might date back to the 1960s, when IBM considered having more persistent controls over files, but decided they had to place too much reliance on physical controls to make it workable. This mirrors the eternal debate between complexity and usability, where usability has always won the day, and security was left out in the cold.
In the mid 90s, InterTrust patented a number of ways of monetising access to information using security techniques, and fought a number of patent battles, more successfully monetising use of their patents than selling products. But the real inhibitor to introducing DRM technology was the lack of horsepower in the desktop PC to manage all the encryption, since most serious volume encryption was done by hardware and not software.
DRM did develop to answer the desires of the film and music industries, until the Content Scramble System was hacked in 1999. But Steve Jobs delivered the nail in the music DRM coffin at Apple, arguing that (in music) everything was sold DRM-free, so why bother with the costs? On the other hand, the Electronic Frontier Foundation (EFF) were trying to make the argument that anything passed over the Internet must be freely accessible for study and comment.
The PDF document DRM saw daylight around 1997 with developments in the print publishing industry, where there was a demand for protecting digital books for general public distribution. However, little attention was paid to business and corporate use and the protection of confidential documents at the time.
It was another step change to use PDF DRM in the corporate environment for commercially sensitive documents, because they had also been relying on domain and network access controls instead of looking at controlling content.
 What features make DRM controls so good for protecting confidential & sensitive information?
What features make DRM controls so good for protecting confidential & sensitive information?

DRM controls are focused on what a document recipient is able to do with the content, where and for how long they can use it for. So content controls are focused on a series of objectives:
Preventing unauthorised access
- encryption to stop unauthorised use
- licensing to identify authorized users/locations
Stopping making uncontrolled copies
- stopping screen grabbing
- stopping copying and pasting
- stopping Save and Save As
Controlling dates when content can be used
- cannot be used before date
- cannot be used after date
- can only be read a fixed number of times or days
Controlling where documents can be used
- restricting use to specific devices
- locking to specific IP addresses or networks
- allow or deny use in specific countries
Identifying the licensed user
- optionally can be viewed with watermarks on the screen;
- optionally can be printed with watermarks on the printout
Controlling document printing
- printing can be prevented
- printing can detect file drivers and refuse to use them
- numbers of prints taken can be limited
Tracking document use
- Log when documents are viewed and printed
- Log when and where this occurred
Controlling metadata
- Sanitize PDF files to remove identifying information from metadata
- Remove annotations, attachments, and JavaScript in one click
Combining these overarching DRM functions allows corporate departments to fine-tune the restrictions that are applied to sensitive documents, whether they are in the corporate domain or not. This is very important since some documents will need to be limited to parts of the internal corporate network (the electronic equivalent of Chinese walls) whilst others must be accessible in foreign domains that the corporate body has no wish to connect directly to at any level.
DRM controls for confidential and sensitive commercial documents can be both by document content and by recipient(s), allowing a very fine-grained approach. Encryption prevents unauthorised users from any kind of use of the contents, including getting control of licenses and applying them to additional machines, unless the information administrator has decided to allow that.
 Why Locklizard to protect your confidential and business sensitive documents?
Why Locklizard to protect your confidential and business sensitive documents?

Locklizard has been developing the advanced document DRM controls we have discussed for PDF documents since 2004 and is a recognized market leader and specialist in the subject.
Our document DRM solutions enable you to protect your confidential and sensitive documents regardless of where they are stored, preventing sharing and leakage. Securely share confidential and commercially sensitive documents and files within an organisation and externally with third parties while retaining full control over their use.
 FAQs
FAQs
Can you share confidential and sensitive documents with SharePoint?
Yes, but you will need to protect them with a DRM solution first, or users may be able to copy, edit, and share your documents with others. For more information on this, see How secure is SharePoint and How to share with external users securely in SharePoint.
How do I protect confidential documents when emailing them?
Use a DRM solution such as Locklizard to protect them, then attach the encrypted file to your email. This will prevent unauthorized users from being able to access your document, and authorized ones from being able to share, edit, copy and paste, or print them.
How does Avast protect sensitive documents?
Avast Sensitive Data Shield is a data loss prevention (DLP) solution that is designed to protect sensitive files on your local hard drive in the event that it is compromised by malware. Like all data loss prevention tools, it does not stop users from sending sensitive documents to others.

 Protect confidential & sensitive documents – stop sharing and leakage
Protect confidential & sensitive documents – stop sharing and leakage Distributing and managing commercially sensitive & confidential documents
Distributing and managing commercially sensitive & confidential documents Confidential document solutions and their drawbacks
Confidential document solutions and their drawbacks PGP encryption
PGP encryption DLP solutions
DLP solutions Cloud document solutions
Cloud document solutions PDF password protection
PDF password protection The problem with most confidential document solutions
The problem with most confidential document solutions Using DRM to protect confidential & sensitive documents – stop sharing and leakage
Using DRM to protect confidential & sensitive documents – stop sharing and leakage What features make DRM controls so good for protecting confidential & sensitive information?
What features make DRM controls so good for protecting confidential & sensitive information? Why Locklizard to protect your confidential and business sensitive documents?
Why Locklizard to protect your confidential and business sensitive documents? FAQs
FAQs
