How secure is Adobe encryption to encrypt PDF files?

Why using Adobe to encrypt a PDF is not secure & superior encryption alternatives
Here, we explore the issues with Adobe Encrypted PDF files and why Adobe PDF encryption is not secure. We also cover why any PDF editor app or online solution that uses password encryption is useless, and how you can encrypt PDFs securely.
Adobe PDF encryption is one of the most popular ways to protect documents, but it has had its fair share of security issues in the past. This blog will look at the state of Adobe encryption today, covering:
- How secure is Adobe PDF encryption?
- Adobe PDF password encryption
- The safety of encrypted PDF files stored locally or in the cloud
- Password sharing and removal
- Password cracking
- Are certificates more secure than password security?
- Encrypting a PDF without Adobe – is it more secure?
- The bottom line: How secure is PDF encryption?
- Safeguard PDF DRM – the best way to encrypt PDF files
 How secure is Adobe PDF encryption?
How secure is Adobe PDF encryption?
If you are looking to encrypt confidential or sensitive business documents, share PDF files securely, or sell PDF files online, then you might want to reconsider using Adobe PDF encryption. While it uses a good encryption algorithm and key strength, the implementation is poor. As of 2025:
- Adobe file encryption does not keep PDFs safe when stored – they can be manipulated and exploited by hackers.
- Password encryption is weak at best and has many manageability and security issues.
- There are no Adobe PDF password requirements. Acrobat warns users when their password is weak, but it does not stop them from choosing it.
- Authorized users can remove the password to open the PDF and then share the unprotected file.
- Unauthorized users can use cracking tools to remove the open password.
- Restrictions to prevent editing, copying, printing, etc. can be ignored or instantly removed.
 Adobe PDF password encryption
Adobe PDF password encryption

Adobe PDF password protection uses two separate passwords to protect a PDF:
Open password
- This is used to encrypt Adobe PDF files (document contents and metadata) and must be entered to open or view it.
- Adobe Acrobat encryption uses an AES 256-bit algorithm, which turns the document into illegible strings of letters and numbers unless the user has entered the correct open password to decrypt it.
- Anybody who has the open password can read the contents, regardless of whether they’re authorized to. There is nothing to prevent users sharing or removing the open password once they know it. They can decrypt the PDF files and share them unprotected in a few clicks.
%22%20transform%3D%22translate(1%201)%20scale(1.95313)%22%20fill-opacity%3D%22.5%22%3E%3Cellipse%20fill%3D%22%23595959%22%20cx%3D%2258%22%20cy%3D%22131%22%20rx%3D%2232%22%20ry%3D%2242%22%2F%3E%3Cellipse%20fill%3D%22%23535353%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(-10.64492%20-14.44348%2020.96088%20-15.44828%2063.1%2045.6)%22%2F%3E%3Cpath%20fill%3D%22%231d1d1d%22%20d%3D%22M49%2078l204%20167%205-261z%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
Permissions password
- This protects the PDF editing, copying and printing restrictions you have set.
- The permissions password does not use encryption to enforce restrictions.
- PDF permissions or restrictions are completely useless – they can be ignored or instantly removed.
In theory, to remove PDF restrictions a user must enter the permissions password. When a PDF reader (e.g. Acrobat Reader or similar) encounters an encrypted PDF file, Adobe’s Security handler checks it against a set a flags to determine what is allowed (viewing) and what isn’t (editing and printing). However, there are weaknesses in Adobe’s security handler. For one, the PDF format itself cannot enforce the restrictions because they are not backed by encryption.
Additionally, as there are more applications to view PDFs than just Adobe Reader, Adobe has to trust third-party developers to build security handlers into their viewers that respect the restrictions. Adobe is not able to enforce this, and notes that applications other than Reader may implement alternate security handlers or none at all.
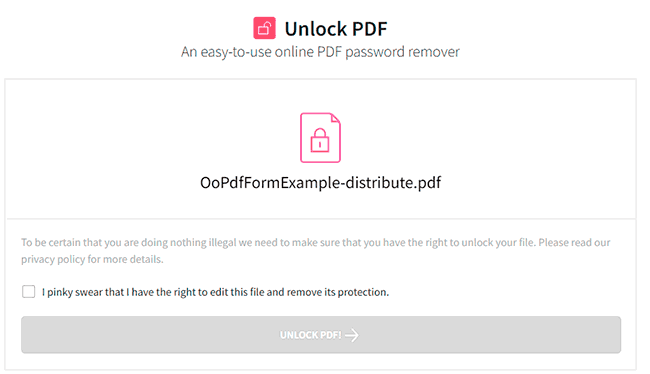
This, combined with other flaws in the Adobe Security handler, means that with minor effort a user can remove PDF restrictions by uploading the file to a free third-party PDF password removal tool, or just open it in a Reader that ignores the permissions (Mac Preview, Google Docs, etc.), making them completely useless.
 Safety of encrypted PDF files stored locally or in the cloud
Safety of encrypted PDF files stored locally or in the cloud
So you have encrypted an Adobe PDF with a strong password, stored it on a server or uploaded it to the cloud, and feel safe in the knowledge that it can’t be hacked. Think again.
Breaking strong encryption on Adobe PDF documents
When you password protect a PDF file using Adobe, it is encrypted with 256-bit AES encryption in Cipher Block Chaining Encryption (CBC) mode. Cryptographically, this is fine, but it’s worth remembering that encrypting a PDF only encrypts the contents of the file. Other information about the PDF, such as the size of its pages, the number of objects, links, etc. are not, which gives attackers a route to circumvent the encryption. CBC also has a known drawback – it does not have integrity control.
Direct exfiltration attack
Researchers across several German universities found that it is possible to exploit CBC flaws by adding content to an encrypted PDF document. As there are no integrity checks, the user would not be alerted to these changes, which could include a submit form function/JavaScript that sends the contents of the PDF to the attacker once it is opened.
Malleability attack
Alternatively, an attacker can exploit the lack of integrity control to change the contents of a cipher block, provided they know part of the plain-text information that was encrypted. Unfortunately, because Adobe both encrypts editing permissions with the file and stores them in the file in an unencrypted plaintext form, attackers always know what some bytes of the file are. They can use this information to manipulate encrypted data to send the contents of a file to a third-party site, etc.
Of course, there are many other malicious things you could do with this power, but we’ll leave that to your imagination.
Results
Okay, so PDF encryption is exploitable, but what is the impact in the real world? Is this limited to a few third-party PDF viewers that nobody has heard of? Unfortunately, not. Every mainstream PDF reader out there can have data exfiltrated with one or both of the methods above. Here are the research’s results:
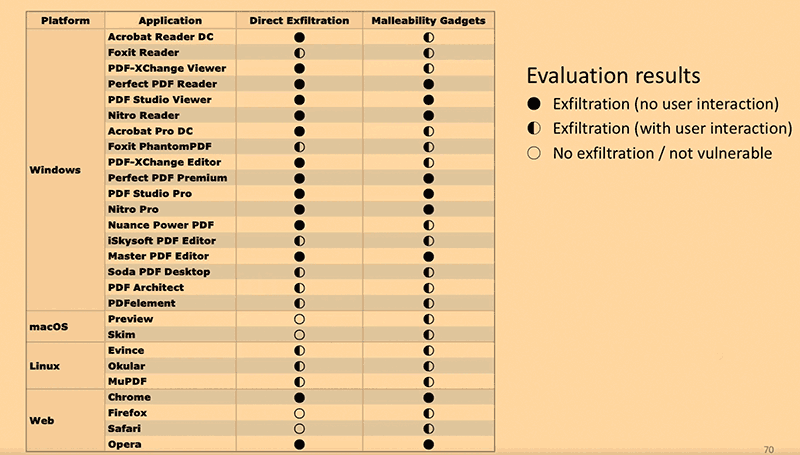
Source: Müller et al.
As you can see, many PDF readers are vulnerable to direct exfiltration without user input, including Adobe’s flagship Acrobat Reader DC. Every PDF reader is vulnerable to malleability attacks in one form or another, however, making Adobe Encrypted PDF files not very secure at all.
If you rely on encryption to protect your PDF’s contents when it’s in transit or at rest, it’s time to think again.
 Password sharing and removal
Password sharing and removal
Perhaps of even bigger concern is how easy it is for somebody who is authorized to open your PDF to give access to somebody else. Adobe Acrobat files are decrypted when the user provides the correct password. No further checks are performed to determine whether the user should have the password – where they are opening it from, whether it is from a recognized device/network, etc.
As a result, anybody who has the password can pass it along with the PDF file to anybody they like (intentionally or via social engineering/phishing). Most PDF readers have no tracking, so you won’t even know that it has happened. Even if they do, tracking is worthless if users can create unprotected copies, convert Adobe PDF to Word and back again to remove tracking pixels, etc.
Alternatively, an authorized user can just remove the PDF password from the file. Anybody that has the open password can remove it using Adobe Acrobat Pro or any number of free PDF password remover tools. They can then share the file as if it were never protected in the first place.
 Password cracking
Password cracking
Removal of the open password by unauthorized users
If you are confident that authorized users won’t share your encrypted PDFs, then what about unauthorized ones? Are encrypted files safe to store, share and sell online?
All passwords are vulnerable to cracking, and it’s no different when they are used in combination with PDF encryption. The important thing to realize is that password cracking is a matter of when and not if depending entirely on password strength. With a complex enough password, you can make that millions of years on current computers with brute force attacks. Use a weak password, however, and that time can be in the milliseconds due to quick dictionary attacks.
Other issues of using passwords to encrypt PDFs
If you just use a password that’s, say, 11 random characters with numbers, upper and lowercase letters, and symbols this problem is solved, right? Well, unfortunately, it’s not as easy as that. You also need to worry about:
- Password management
Different PDFs need different passwords, otherwise you have a single point of failure. When you consider the hundreds of documents businesses process each day and the need for secure storage and fallbacks, this quickly becomes cumbersome and expensive. - Poor password hygiene
The more complex a password is, the harder it is to guess or brute force, but the harder time users have to remember it. This often leads to them either choosing an insecure one (there are no adobe password requirements), or noting it down insecurely. If you do put a “forgot password” system in place, that means more strain on your IT department and the potential for that system to be exploited, too. - Phishing and social engineering
Brute-forcing isn’t the only way to get a password. Users can be tricked into giving even the most secure password via social engineering or phishing attacks. It’s better if the user has no password they can share so that the attacker has nothing to steal.
What about the PDF permissions password?
As we mentioned earlier, the Adobe PDF permissions password does not utilize encryption. Rather, it’s a set of controls that informs the PDF viewing application which options it should grey out.
There are two major problems with this approach:
- Firstly, as the permissions are not backed up by cryptography, they are trivial to remove. There are numerous online and offline applications that will remove Adobe PDF permissions in seconds. Editing and printing are quickly restored.
%27%20fill-opacity%3D%27.5%27%3E%3Cellipse%20fill%3D%22%23cacaca%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(-284.13025%20-3.47148%20.58718%20-48.05905%20239.8%20329.3)%22%2F%3E%3Cellipse%20fill%3D%22%23cacaca%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(42.92025%20-23.94165%2017.8636%2032.0241%20287.9%201.2)%22%2F%3E%3Cellipse%20fill%3D%22%23fff%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(580.41524%2039.2298%20-8.64753%20127.94259%20364.7%20165.8)%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
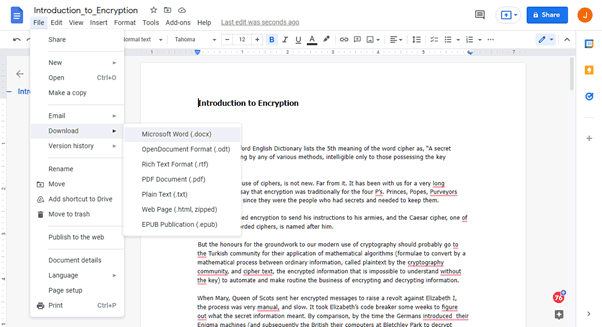
- The second issue is with enforcement. For Adobe permissions to work, the PDF reader application needs to have a mechanism through which it can disable certain functions. Adobe’s system naively trusts that third-party PDF reader developers will take the time to implement its controls. You can see the results for yourself: just open a permission-protected PDF in Mac Preview or Google Docs. No restrictions at all and minimal effort is required.
%22%20transform%3D%22translate(1.2%201.2)%20scale(2.35156)%22%20fill-opacity%3D%22.5%22%3E%3Cellipse%20fill%3D%22%23cbcbcb%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(-70.8%20147.4%20-37.3)%20scale(48.14317%2059.12228)%22%2F%3E%3Cellipse%20fill%3D%22%23fff%22%20cx%3D%2226%22%20cy%3D%2250%22%20rx%3D%2272%22%20ry%3D%2272%22%2F%3E%3Cellipse%20fill%3D%22%23cdcdcd%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(115.2%20118.1%2079.8)%20scale(14.52105%2027.38362)%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
We cover in detail the ways you can bypass or remove protection in our blog on How to edit a password protected PDF.
 Are certificates more secure than password security?
Are certificates more secure than password security?

Encrypting a PDF with a certificate is more secure than using Adobe PDF password encryption (especially if you want to send a PDF securely). This is because the recipient must have a private key to decrypt it. Unlike the sharing of passwords, users won’t be as keen on sharing their private keys. However, once the PDF is decrypted it can be saved as an unprotected file. Permissions to restrict editing, etc. can then be easily removed.
Our blog on PDF password or certificate encryption covers which is the best security method.
Digital signatures vs encryption
Certificates also allow PDFs to be digitally signed. Digital signatures have their place, particularly when combined with other security mechanisms so that they cannot be easily removed. However, the key thing to understand is that digital signatures are for verifying that the copy of the document you have matches the original. By themselves, they do not stop sharing or editing, and they generally only use partial encryption. This is much weaker than full encryption, as the presence of unprotected code can make it possible to insert unencrypted information that remains undetected.
You can read about the vulnerabilities of digital signatures in detail in PDF Digital Signatures & Encryption.
 Encrypting a PDF without Adobe – is it more secure?
Encrypting a PDF without Adobe – is it more secure?
Acrobat isn’t the only PDF encryption software, but are the others any more secure? Usually, no. Third-party PDF encryption tools must conform to the PDF specification and use the Adobe Security Handler if they want files to be openable in all PDF viewers and editors. As a result, they still use passwords, and they still have the same flaws. In other words, if an encrypted PDF can be opened in Acrobat PDF reader, then it is just as useless.
Despite many software providers’ claims of ‘high security’, they cannot stop editing, either. A prime example is demonstrated in how to make a PDF not editable, where all the solutions fail to mention that it is just as simple to remove their read-only protection as it is to apply it.
 The bottom line: How secure is PDF encryption?
The bottom line: How secure is PDF encryption?
Encrypting a PDF with a password is useless
PDF encryption software that uses passwords to encrypt PDF files is useless and should not be used for confidential or sensitive document protection. This is true whether it is Adobe Acrobat or a third-party PDF encryption app or online solution – they all rely on the PDF standard and Adobe’s security handler, so have the same weaknesses.
Encryption algorithm and strength does not mean better security
The encryption algorithm and strength – AES vs RSA, and key size – 128-bit vs 256-bit, etc. is important, but so too is the way it is implemented in apps and services. Adobe PDF encryption is one example where poor implementation can lead to disastrous results.
Secure implementation is key for document protection
Adobe encrypted PDF files just have too many flaws to be used for the protection of sensitive or confidential data. They are of limited use when a PDF is in transit and at rest due to exfiltration attacks, and they don’t stop sharing, copying, editing, or printing because passwords can easily be shared and permissions removed in seconds.
Online solutions expose you to additional risks
Uploading your unprotected PDF documents online exposes them to a third-party and potential compromise on a cloud server. Solutions that encrypt a PDF online should therefore not be used for important, sensitive, or confidential business documents.
The only secure way to encrypt a PDF is without passwords
Locklizard for example, encrypts PDFs without passwords so there are none to share or remove, uses digital rights management controls, and a secure viewer to enforce restrictions and prevent removal.
Ultimately, the PDF format was not built with security in mind. Indeed, it wasn’t until after its initial release that Adobe tacked on some half-hearted controls. The focus from the beginning has been on convenience and shareability, and despite Adobe’s best efforts, encrypted PDFs are still very shareable and can be copied and edited even if protected.
Instead of relying on Adobe or similar password apps to encrypt PDFs, businesses should look to purpose-made security software to protect their PDF files.
 Safeguard PDF DRM – the best way to encrypt PDF files
Safeguard PDF DRM – the best way to encrypt PDF files
Locklizard Safeguard DRM protects files without passwords or certificates, instead locking PDFs to specific devices using a combination of AES 256-bit encryption, transparent key management, licensing controls, and a secure viewer application to enforce restrictions.

Safeguard prevents:
- Unauthorized users from opening files: Users can only open a PDF if they have a valid license file activated on their PC or mobile device. A license file can only be installed on one device (unless otherwise configured).
- Authorized users from sharing file’s encryption key: The keystore is encrypted and does not function if moved or copied to another device.
- Content extraction: Copying (copy and paste), screenshots, and PDF printing are disabled by default. Physical printing can also be disabled or limited.
- Editing: The Safeguard PDF viewer application does not have editing functionality built-in. Users cannot open PDFs encrypted with Safeguard in any other application, nor can they extract the content, and therefore they cannot edit the file.
- Printing: Prevent printing or limit prints to a certain number of copies, black and white, or grayscale.
- Use after a defined period: Safeguard PDF allows you to expire documents after a certain date, number of days from first open, number of prints, or number of opens. You can also revoke PDF access manually at any point.
- The sharing of phone pictures and printed copies: Locklizard Safeguard comes with a dynamic watermarking system. You can protect a document with a watermark and add variables like name and email address. These variables will then be automatically adjusted to match the user when they open the document. They won’t be able to share any version of it without having their name and email address clearly on show. Unlike Adobe watermarks that can be simply removed, Locklizard’s are permanent.
- Untraceable usage: Tracking tools allow you to see how many times your document was opened and printed, by whom, and where from.
Locklizard provides the ultimate in PDF protection, ensuring your PDF documents are encrypted and secured from unauthorized access and misuse, both online and offline in any location.
You can read more about Safeguard and its features here. Or, to add security to your PDF without passwords and protect your royalties or sensitive information, take a 10-day free trial of our DRM software.
 FAQs
FAQs
How secure is Adobe PDF encryption?
Adobe PDF encryption that uses passwords is not secure. Encrypted files can be manipulated at rest, users can share or remove the password required to access the PDF, and permissions or restrictions can be ignored or instantly removed using free online tools or software.
Using certificate encryption is equally useless if you want to prevent sharing. Authorized users can decrypt the PDF, instantly remove any restrictions and then share the document with others.
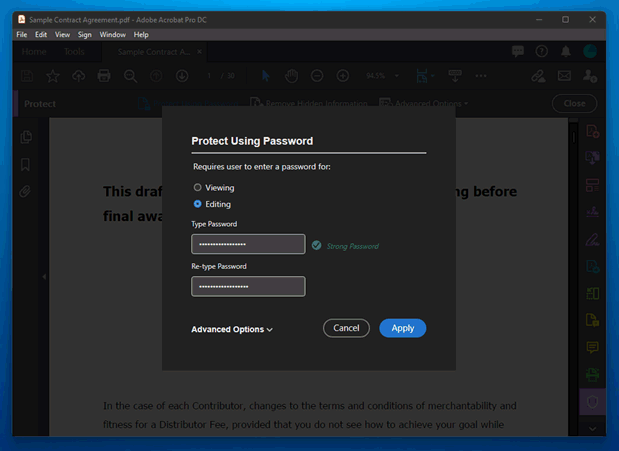
How do you encrypt a PDF with Adobe Acrobat?
- Open a PDF document in Adobe.
- Select from the Menu option ‘Protect using Password’.
- Enter a password to encrypt the PDF for viewing (opening).
- Optionally select the Advanced Options to choose between password or certificate encryption.
%22%20transform%3D%22translate(1%201)%20scale(1.95313)%22%20fill-opacity%3D%22.5%22%3E%3Cellipse%20fill%3D%22%23595959%22%20cx%3D%2258%22%20cy%3D%22131%22%20rx%3D%2232%22%20ry%3D%2242%22%2F%3E%3Cellipse%20fill%3D%22%23535353%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(-10.64492%20-14.44348%2020.96088%20-15.44828%2063.1%2045.6)%22%2F%3E%3Cpath%20fill%3D%22%231d1d1d%22%20d%3D%22M49%2078l204%20167%205-261z%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
Can you encrypt Adobe PDF files with Adobe Reader?
No. With Adobe Reader you can only view, print and comment. You have to upgrade to Acrobat Pro to encrypt files.
To encrypt a PDF for free with Adobe upload it to their online tool and enter a password to restrict access. You cannot add editing or other restrictions with the free version.
Because you have to store your unprotected document on Adobe’s servers, it is not advisable to use this tool to protect sensitive content. This is equally true of other online solutions that require you to upload unprotected files to their servers.
Is it easy to break strong encryption on Adobe PDF documents?
Yes, if a weak password has been used, users can use a password removal tool to crack the PDF password. Note that this does not break the encryption algorithm, it just removes the password that was used to encrypt the file.
Hackers can also exploit Adobe encrypted PDF documents due to poor implementation and lack of integrity control.
Can you use other software to encrypt Adobe PDF files?
Yes, there are lots of PDF encryption sites that let you encrypt Adobe PDF files online for free, but you usually have to pay to add restrictions. However uploading confidential or sensitive files to a cloud server that is not under your control is generally unwise since unprotected files are at risk of being stolen.
A more secure option is to download software and install a PDF editor to encrypt Adobe PDF files locally on your device – unprotected copies are therefore not exposed online. Again, paid versions give you access to more functionality.
Both online solutions and installed apps however do not offer any better protection than Adobe Acrobat. They all use passwords to encrypt Adobe PDF files to restrict access or viewing, and permissions are not backed by encryption and therefore can be easily removed.
How do you open an encrypted PDF?
Open the encrypted PDF in Adobe reader or any other PDF reader app and enter the Open password. If you have forgotten the password then you can use a password cracker to remove it – the weaker the password the quicker it will take.
Does Adobe encryption and decryption use the same key?
Yes, the key used for encryption and decryption is the password. The password entered to encrypt the PDF is also the same password used to decrypt the PDF files.
Can you open an Adobe encrypted file on Kindle?
No. It is not possible to open and read Adobe encrypted PDF files on the Kindle.
Does Adobe Digital Editions provide better file encryption?
No, it can be instantly removed – see Adobe Digital Editions DRM.
Is Adobe encryption HIPAA compliant?
Acrobat includes several security features designed for HIPAA compliance, such as encryption, password protection, and audit logs that record document access and modifications. However, to ensure HIPAA compliance, healthcare organizations must proactively activate these security measures and restrict document access to authorized individuals only. Additionally, providing staff with adequate training on effectively utilizing these security tools is crucial for safeguarding patient information and maintaining regulatory compliance.

 How secure is Adobe PDF encryption?
How secure is Adobe PDF encryption? Adobe PDF password encryption
Adobe PDF password encryption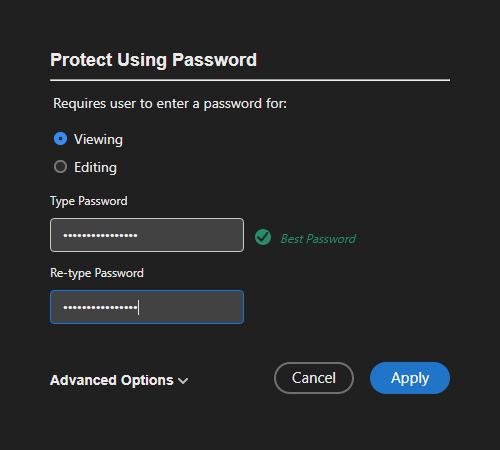
 Password sharing and removal
Password sharing and removal Password cracking
Password cracking
 Are certificates more secure than password security?
Are certificates more secure than password security? Encrypting a PDF without Adobe – is it more secure?
Encrypting a PDF without Adobe – is it more secure? The bottom line: How secure is PDF encryption?
The bottom line: How secure is PDF encryption? Safeguard PDF DRM – the best way to encrypt PDF files
Safeguard PDF DRM – the best way to encrypt PDF files FAQs
FAQs
