PDF Protection method
The first question to consider when creating a secured PDF is how easy it is for others to remove the security.
The most popular method for creating secured PDF files was and still is password protection, but passwords are easily removed using any of the PDF password recovery programs – see PDF Encryption & Security. If you truly want to secure your PDF files, passwords are clearly not the way forward.
Some businesses use secure document sharing sites such as secure data rooms but these have many security weaknesses. Users can share login info, and modify or disable JavaScript to remove protection. See Google Docs Security as an example of how easy it is to remove security from a PDF file and other document formats.
Adobe Content Server used PKI technology to replace passwords – see password or certificate encryption – but that meant that the publisher needed the customer’s public key in order to create a unique secure PDF file. When using its PKI, a PDF file had to be protected independently for each individual recipient. The same PDF file could end up being secured hundreds or thousands of times depending on how many recipients there were. This was not a readily scalable architecture, particularly if your business went global.
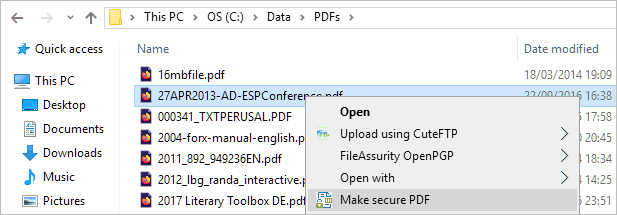
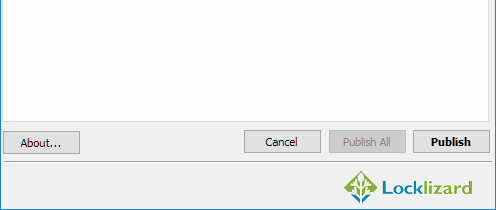
Locklizard DRM secured PDF files only need to be encrypted once and use long and random encryption keys. Decryption keys are required for authorized users to open protected PDF documents. They do not travel with the PDFs themselves but are instead transparently relayed securely to the recipient’s device and stored encrypted in a keystore. There are no passwords for users to enter so there are none to share, and users don’t have to send their public key to anyone.









 Free Trial & Demo
Free Trial & Demo Securing PDF documents and files
Securing PDF documents and files





 Why passwords make for poor security
Why passwords make for poor security How to print a secured PDF
How to print a secured PDF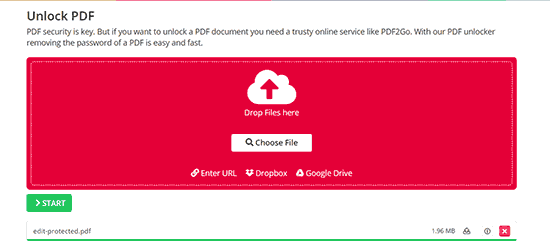
 How to save a secured PDF
How to save a secured PDF
 How to edit a secured PDF
How to edit a secured PDF
 How to copy text from a secured PDF
How to copy text from a secured PDF




 FAQs
FAQs