Doc Tracking: Track document opens & prints, control use

Tracking Documents and Controlling Use
Why track documents?
Seeing who has opened or printed electronic documents is at the heart of compliance and due diligence. For corporate bodies, being able to say if a document has been used or not and if so, by which authorized users, and whenit took place, is critical to demonstrating that it has been seen by the recipient and not just delivered.
Document analytics is another useful area – seeing what documents are most viewed and printed in real-time and what is of interest to individual users.
What is a document tracking system?
Document tracking systems enable the tracking functionality mentioned above while often helping admins to find, manage, and control documents. There are varying approaches to the implementation of this technology that can result in significant differences in accuracy.
 Free 10 Day Trial
Free 10 Day Trial
Track & Control PDF Documents
- Track document views and prints
- Stop unauthorized access and sharing
- Control use – stop copying, editing, printing, etc.
- Lock PDFs to devices, countries, locations
 | Track Documents & Control use with Safeguard PDF Security |

Tracking documents has never been easier. Safeguard PDF Writer allows you to add open and print tracking to your documents in just a few clicks.
Log and tracking data is presented to you in a readable format in the Safeguard Admin system, with charts, timestamps, and other useful information.
 How to track documents
How to track documents
- Right-click on a PDF on your desktop and select ‘Make Secure PDF’.
%22%20transform%3D%22translate(1%201)%20scale(2.11719)%22%20fill%3D%22%23fff%22%20fill-opacity%3D%22.5%22%3E%3Cellipse%20cx%3D%22224%22%20cy%3D%221%22%20rx%3D%22133%22%20ry%3D%2229%22%2F%3E%3Cellipse%20cx%3D%22244%22%20rx%3D%22138%22%20ry%3D%2230%22%2F%3E%3Cellipse%20cx%3D%2224%22%20cy%3D%223%22%20rx%3D%2229%22%20ry%3D%2216%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
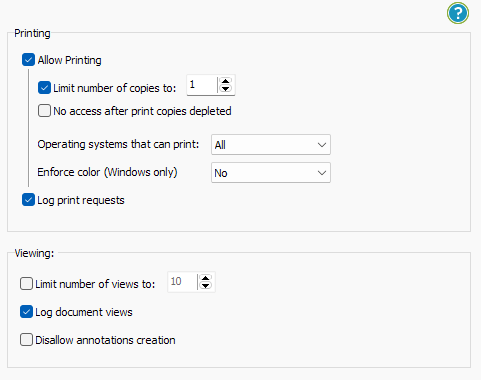
- In Safeguard Secure PDF Writer, go to the Printing & Viewing tab:
- To track document opens, check the box ‘log document views’
- To track document prints (if you have allowed printing), check the box ‘log print requests’
%22%20transform%3D%22translate(1.3%201.3)%20scale(2.60547)%22%20fill-opacity%3D%22.5%22%3E%3Cpath%20fill%3D%22%23ccc%22%20d%3D%22M-8-16L2%20271%2086%2069z%22%2F%3E%3Cellipse%20fill%3D%22%23d2d2d2%22%20cx%3D%2231%22%20cy%3D%22246%22%20rx%3D%2224%22%20ry%3D%2263%22%2F%3E%3Cellipse%20fill%3D%22%23fff%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(-78.79662%20-15.69423%2038.09074%20-191.24355%20143.6%20154)%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
- Press the Publish button to protect the PDF.
%27%20fill-opacity%3D%27.5%27%3E%3Cellipse%20fill%3D%22%23d1d1d1%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(-111%20281.7%2044.2)%20scale(118.5027%20479.12104)%22%2F%3E%3Cellipse%20fill%3D%22%23fff%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(79.3%2088.3%20174.7)%20scale(155.21088%20329.48763)%22%2F%3E%3Cellipse%20fill%3D%22%23d5d5d5%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(-26.9%20639.1%20129)%20scale(85.44075%20134.12546)%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
- Select the users you want to give access to your secured document using the cloud-based Admin System:
%27%20fill-opacity%3D%27.5%27%3E%3Cellipse%20fill%3D%22%2355c4df%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22rotate(90.2%20107.3%20141)%20scale(43.64149%20572.09553)%22%2F%3E%3Cpath%20fill%3D%22%23fffffe%22%20fill-opacity%3D%22.5%22%20d%3D%22M-73.4%20560.4l-79.9-346%20412.5-95.2%2079.8%20346z%22%2F%3E%3Cellipse%20fill%3D%22%23d8d2d1%22%20fill-opacity%3D%22.5%22%20rx%3D%221%22%20ry%3D%221%22%20transform%3D%22matrix(-12.04925%20-60.99846%20128.61015%20-25.40483%20192%20305.4)%22%2F%3E%3C%2Fg%3E%3C%2Fsvg%3E)
- Distribute your protected PDF document just like any other file.
For a more detailed look at the process, you can read our full guide on how to add security to a PDF.
 Document Tracking Software
Document Tracking Software
Using Enterprise PDF DRM Security you can track documents and monitor use.
- See what users are opening your documents
- See where they are being used and how often they are being viewed
- See when they are being viewed and printed
- Track print usage – how many prints, when and from where
- Track documents regardless of where they are stored or who they are sent to
- Apply location locking controls if documents are being opened from unauthorized locations
- Instantly revoke documents if you think they are being misused
 | Why Safeguard to Track Documents? |

Using Safeguard to track documents vs Document Tracking systems
As well as tracking document use, Safeguard PDF Security enables you to:
- Prevent users from saving to other file formats to remove tracking controls
- Stops users sharing PDF documents and editing, copying, and pasting content
- Disable printing (another easy way to remove tracking, especially if users can print to PDF files)
- Lock PDF documents to specific devices and locations
- Make PDFs expire on a specific date, after a number of opens or prints, or after a number of days from opening
- Stop screen-grabbing applications and Windows print screen from taking screenshots
- Watermark viewed and printed pages with dynamic user and system data
- Revoke documents at any time if you think they are being misused
Safeguard PDF security is much more than a document tracking system – it enforces doc tracking controls and enables you to distribute and/or sell PDFs securely and control their use regardless of their location.
Tracking overall use


Tracking document views


Tracking document prints

 | Control & track document use with DRM protection |
 Document Tracking Services
Document Tracking Services
Document tracking might not sound like an exciting subject to your average joe, but in the retail world, it can be intoxicating. Ever since supermarkets discovered loyalty cards, knowing what users are doing has been valuable. Suddenly, they could both market items to consumers that they had already bought, and contrast their habits with similar people to see what they might want to buy in the future.
Now, you may have varying personal opinions on whether or not this is a good thing. The feedback marketers have heard time and time again, however, is that users are (generally) friendly towards advertisements when they pitch them a product they actually want.
When it comes to document tracking, there is an opportunity to gain context. A seller can glean how often a book is opened (or printed if allowed) and therefore assess whether it’s a product they actively engage with. Open and print statistics can also provide valuable data on a document’s popularity over time at a global level.
But document tracking for commercial purposes, whilst it mimics supermarket tracking and the web analysis of the search engines, is probably at a lower level than the element of document control and tracking that the corporate enterprise would find useful.
 Tracking Document Use in the Enterprise
Tracking Document Use in the Enterprise
For the enterprise, document control is essential. Far too many internal documents contain confidential information, whether that’s information that is subject to regulatory control or is a secret that you do not wish to find on a download site.
For the corporate, document tracking – who exactly was authorized to see this and when (if ever) it was opened, can be amazingly useful information, especially once you understand that electronic evidence can be just as good as any other kind.
Imagine that, after an error of some sort, an employee is asked – “Did you see the instructions concerning the security of this document?”. With document tracking, an enterprise can see that the document was at least opened, and is therefore entitled to come to the conclusion that it must either have been read or ignored. Valuable insight indeed.
Knowing the location at which a document is opened can be interesting, too. If top secret documents are frequently being opened from someone’s home, you probably need to have a bit of a talk. Or, you might want to start using DRM to stop documents from working outside of an office location.
In the corporate world, doc-tracking is therefore seriously interesting from many perspectives. It complements document control, without which, you don’t have anything at all.
 | Document Control & Doc Tracking |
Establishing document control is just the beginning of wisdom. If you cannot achieve document integrity – that the document delivered must be the document sent in both form and format, then you are building on sand.
What document tracking builds on top of document control is the ability to know when particular events (usually the opening of a document, but also the printing of a document) took place. What it cannot tell you is when someone stopped using a document.
There are many reasons for this. On the Internet, if a computer dies on you (or just gets disconnected from the Internet) the protocol has no method of noticing. As a logging system, there are no messages that say, “I have recently died”, or, “This application is no longer talking”. Imagine the horrifying amount of network traffic that would be generated if applications were continually confirming their existence – never mind the problems of managing it all. It is technically feasible, as are most things, but not technically wise or sound.
For any of this to be useful, however, document control is an absolute, a must. Without it, any document of any importance can be distributed anyhow, anywhere, at any point. Document tracker systems are a building block on top of document control that can be and is a valuable tool in a wide number of circumstances. If you believe that it will deliver valuable marketing information, it may prove informative. But if you need to be able to ‘prove’ that internal users actually received and at least opened (or did not open) documents then document tracking is invaluable.
 Is tracking document downloads enough?
Is tracking document downloads enough?

Some organizations will wonder if they really need to track every single view and print. And it’s true, if you’re selling a document to a consumer or do not need to worry too much about its compliance, you may not need to know every time it is opened. Tracking document downloads can seem like a good middle ground – allowing you to perhaps notice if somebody has shared their link with others or spot unusual activity.
The reality, however, is that tracking document downloads is usually a waste of time. It doesn’t give a good idea of how often, where, when, or on what device your documents are being used. Users frequently create multiple copies of a document to transfer to different devices or share with others. For this same reason, it’s also useless as a tool to spot misuse. A user does not need to share the link because they can just send a copy of the downloaded document directly instead.
Ultimately, then, it is not a valid method of document control, and it is useless for compliance. It’s perhaps better used as a tool to help diagnose server performance.
 How effective are tracking pixels in documents?
How effective are tracking pixels in documents?

Tracking pixels are used quite commonly in email communication, where they are embedded in the sender’s message and phone home once the email is opened. As a result, many believe that using a tracking pixel for technical documentation, board minutes, contracts, etc. is also a good idea. The reality, however, is that the two mediums have fundamental differences that require fundamentally different approaches.
Unlike a received email, a document is designed to be modified. This allows any recipient who receives a Word document with a tracking pixel to find it and remove it. There are various ways to identify tracked pixels in documents, whether it be by changing the background color, using the word processor’s developer tools, or searching the document’s code. If the user is aware that you may be tracking them, then in the best-case scenario your tracking pixel will work only the first time they open the document and will then be promptly removed. In the worst case, they’ll remove the code before even opening the document in the application of choice.
So, tracking pixels may be a useful tool in emails, but without something to stop them from being removed, they are not a serious security mechanism.
 Why document tracking needs DRM
Why document tracking needs DRM

Enforcing doc-tracking with Digital Rights Management
Although there are many tracking solutions available, if a user can save the document to a different file format, edit the file, or print to PDF then the tracking can be easily bypassed and is essentially moot. The same is true if users can copy and paste the content into other applications.
It is often also impossible to establish who you are actually tracking. If users download a document, then they can share it, and if they log in to a web portal to view a document then they can share login credentials with others. IP data is usually unreliable since users frequently change their IP addresses or can share the same IP with multiple users via a VPN. Proxy services also enable users to mask their real IP.
What is the best way to track documents?
By using document DRM to enforce tracking controls, you can prevent users from saving to different file formats, disable printing, restrict editing, and prevent copy and paste. Most importantly, you can lock documents to authorized machines or devices. This means that for an unauthorized user to view the document they must have access to the physical device. You can therefore be much more certain that tracking is being enforced and which user you are actually tracking.
 Download Document Tracking & Control software
Download Document Tracking & Control software

PDF Document Tracking: Track Document Opens and Prints with Safeguard Enterprise
Download document tracking software with DRM controls that protects and controls documents published in PDF format.
Through the use of US Government strength encryption (AES) and digital rights management controls to prevent unauthorized use and misuse of your documents, you control who views your documents, what they can do with them (copy, print, etc.), and when they can no longer be viewed (expire). Track when documents are opened and printed and when and where this occurred. Provide an audit trail for compliance purposes. Revoke access instantly if you think documents are being misused.
See our customer testimonials or read our case studies to see why thousands of organizations use Locklizard PDF security to securely distribute their documents.

 How to track documents
How to track documents

 Document Tracking Software
Document Tracking Software Document Tracking Services
Document Tracking Services Tracking Document Use in the Enterprise
Tracking Document Use in the Enterprise Is tracking document downloads enough?
Is tracking document downloads enough? How effective are tracking pixels in documents?
How effective are tracking pixels in documents? Why document tracking needs DRM
Why document tracking needs DRM Download Document Tracking & Control software
Download Document Tracking & Control software FAQs
FAQs















