

Protect PDF files: is password encryption, certificates or DRM best?
 | Choosing the right PDF protection software |
There are many software solutions you can use to protect PDF files in a business environment. Here we review some of the most popular PDF document protection systems, and how they can be used to lock PDF files from opening and control their use.
The choice of software used depends on the reasons why the PDF files need protecting. The content may be:
- commercially confidential
- personal data defined by regulations such as HIPAA or GDPR or the new Chinese PIPL. These will all require different solutions where personal data flows across borders
- trade secrets
- intellectual property
With any business, there will need to be some mechanisms to exert control over the distribution and subsequent use of protected documents, some of which may be inside an organization, some within cooperating organizations and some to individual recipients including the general public.
For example, you may want to:
- stop training courses from being shared
- prevent ebook piracy
- secure reports and analyses
- protect research data
- stop document leakage
- enable secure external document sharing
- Automatically expire documents to comply with document retention policies
Regardless of the above your PDF documents will need protecting to ensure they cannot be accessed by unauthorized users or misused by those that have been given access.
We shall now cover the use of passwords and certificates for PDF encryption and access control, and the use of PDF restrictions and DRM (Digital Rights Management) that provide granular protection over PDF use.
 | Protecting PDF files with passwords |

At the most basic level there is PDF password encryption or password access control. The PDF file is encrypted with a password and in theory, only a recipient with knowledge of the password used to protect the PDF can decrypt it and open it.
When you encrypt a PDF with a password you can apply two different types of password:
- Document open password
- PDF permissions password
The Document open password is what a user must enter to open the PDF (so you need to give this to users you want to share the PDF with) and the PDF permissions password is used to protect whatever restrictions you set on the PDF document.
 What do PDF restrictions do?
What do PDF restrictions do?
By applying PDF restrictions, in theory, you can restrict what users can do with a PDF document once they have opened it.
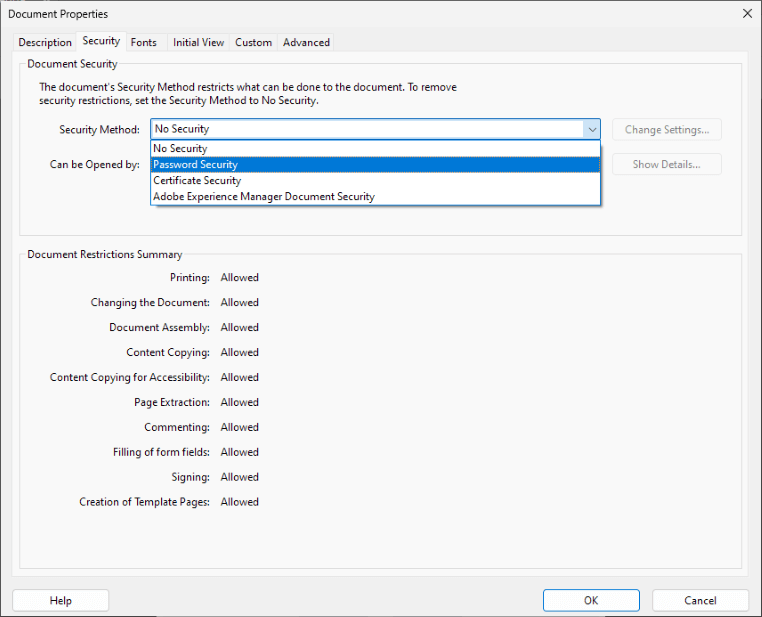
The following PDF restrictions can be set:
- Disable Print
- Enable Print but allow only low-quality prints or high-quality prints
- Prevent changing of content
- Inserting, deleting and rotating pages
- Filing in form files and signing forms
- Commenting
- Stop copying of text and images
 | How effective are PDF restrictions? |
They are completely useless – there is NO point in adding them.
Once a user can open the document, they can remove all PDF restrictions or permissions you have applied by using freely available password removal or recovery tools.
This process is as simple as uploading the PDF to one of these sites (or downloading a program such as Advanced PDF Password Recovery) and selecting the option to remove restrictions.
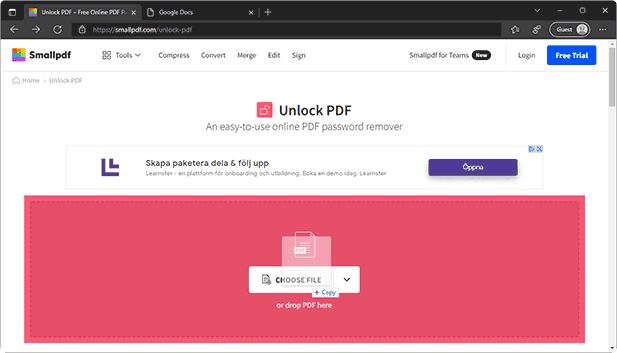
Removing a PDF password and permissions with Small PDF
 Why can PDF restrictions be so easily removed?
Why can PDF restrictions be so easily removed?
This is because of the way the Adobe Acrobat Security Handler was designed (the front door is locked but the back is left wide open) and is based on the honor basis. The PDF specification specifies that all PDF Readers are expected to support the Acrobat Security Handler, but if some don’t, like Mac Preview, Google Docs, and some PDF Readers, then users can just use those applications to view PDF documents and no restrictions are applied.
 Are PDF passwords secure?
Are PDF passwords secure?
No because they have many issues.
If you are not worried about applying PDF restrictions (well there is no point anyway), then you may think that using a document open password to ensure only those users you want to share a PDF securely with is good enough protection. You would however be wrong.
The problems with passwords is that they can be given away so they represent little in the way of PDF Document protection:
- Once you have given a user the document open password, you cannot prevent them from sharing it with others.
- You also have no idea how many people they have shared it with.
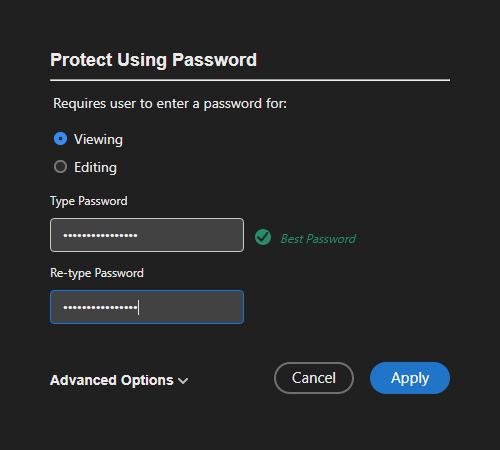
Encrypting a PDF with a password using Adobe Acrobat
However, even if users don’t give away passwords, if someone gets hold of your protected PDF file it is possible for them to carry out a ‘brute force’ attack on the password. Password crackers use this approach along with dictionary attacks and other commonly used passwords – they try using every possible password combination to open the PDF. The shorter and less complex the password (i.e. one that does not contain special characters) the easier and quicker it is to crack. Increasingly, graphics cards are used to do the work of brute force attacks as they tend to be more powerful than CPU chips.
So in summary:
- PDF documents and their passwords can be shared with others
- PDF passwords can be removed with password crackers
- PDF restrictions are totally useless since they can be easily removed or ignored
 Which encryption algorithm is strongest?
Which encryption algorithm is strongest?
AES 256 bit encryption is your best choice because the AES algorithm is NIST approved and a 256 key length is the largest key size you can select.
However, if you are going to protect a PDF with a password then make sure you choose the compatibility option “Acrobat X or later”. This is because in Acrobat 9, Adobe made it a whole lot easier to brute-force attack passwords – Adobe made just one call to verify the password for AES 256-bit encryption compared to 71 in Adobe 8 using AES 128 bit. So, you might think you are applying stronger protection when you are actually doing the opposite.
 Additional issues with password encryption
Additional issues with password encryption
Another weakness in the password encryption approach to PDF document protection is the need to carry the passwords, or an encrypted form of the passwords along with the PDF document such that an attacker can scan the code around a password to see if it can be avoided (jumping round it because it does not encrypt/decrypt the actual document). Some hackers use this approach to extract information related to a PDF document and this is how PDF restrictions can be ignored by various PDF Readers.
Other weaknesses with passwords are the difficulties in managing the scheme:
- creating unique passwords for each PDF file and maintaining a list of them
- distributing the passwords using a secure method (obviously you do not want to email a PDF file along with the password to decrypt it)
- making them human usable – how many people can accurately type in a 20-character password of upper and lower, numbers and special characters? Hence the growth in the popularity of password wallets and the problems of managing them
Unfortunately, passwords will be with us for many years to come because they do not require a complex registration process to support them such as with certificates.
 | Protecting PDF files with certificates |
A more secure alternative to PDF password encryption is to use certificate encryption. A certificate is usually issued by a Certification Authority and contains a user’ public key and additional information such as the issuer and what it was issued for.
Every public key has a corresponding private key which is never distributed to others. Users can create their own public and private key pairs using a key generation program rather than paying a Certification Authority – the certificates are then self-signed and it is up to the person protecting the PDF to decide whether the certificate is genuine (i.e. is for the person they think it is).
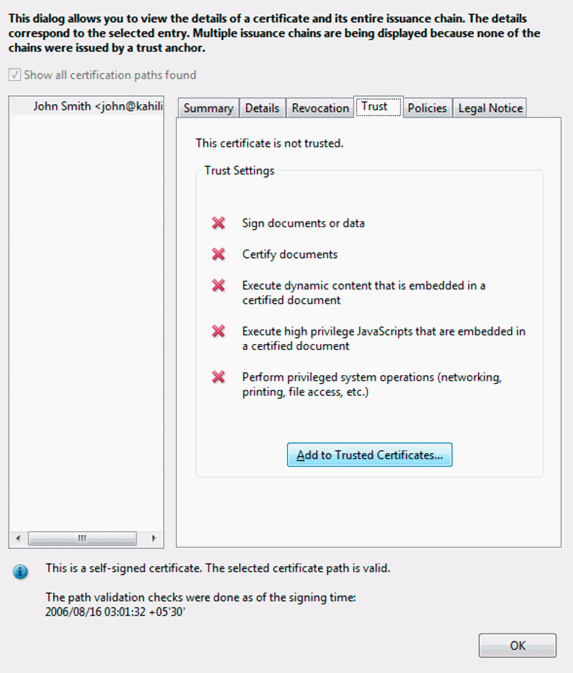
A digital certificate that is self-signed
When using certificate encryption, the PDF file is still protected using a password (for example if AES 256-bit encryption is used then a random 32-byte password is used to protect the PDF), but the password is encrypted using the recipient’s public key. Only the corresponding private key can decrypt it. So, certificates are just a secure key exchange mechanism – there are no passwords to distribute or for users to share with others. The use of certificates is therefore more secure for distributing PDF files since you don’t have to worry about how to transmit the password securely to other users. However, once a user has decrypted the PDF, they can do what they want with it, including saving it to an unprotected file and removing all restrictions using a Password cracker.
 What do Digital Signatures do?
What do Digital Signatures do?
With certificate encryption, users can also use their private key to digitally sign a PDF to assure recipients that the document came from them (assuming of course the certificate is not self-signed).
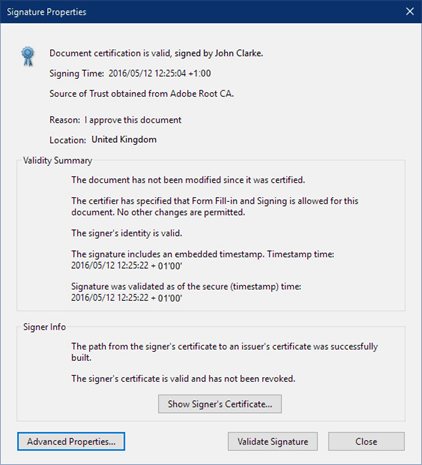
Digital signature information
In theory, if a PDF is digitally signed, then the recipient should be able to also verify it has not been tampered with. Unfortunately, due to weaknesses in signature validation implementations, PDF documents can be altered after signing to trick PDF viewers into displaying content that looks different to the one that was signed and the PDF is not reported as being tampered with.
 Is certificate encryption more secure than password encryption?
Is certificate encryption more secure than password encryption?
Well certificate encryption can be more secure if you trust the recipient and they do not want to distribute the PDF further since the keys are more difficult to attack – currently password cracking applications don’t offer to crack PDF files that have been encrypted with certificates. Also, the PDF can be digitally signed so you know who it originated from which may be important if users are downloading it from a cloud server.
However, if you are looking to sell a PDF document (say an ebook, training course, or report) then certificate encryption is not going to be a good solution for your business because you need the user’s public key before you can send them the PDF. Similarly, if you are going to protect PDF files for internal use, users must have key pairs already generated, and ideally certificates stored in a directory server so they are easily accessible for use.
And lastly, you need to bear in mind that PDF restrictions can be trivially removed regardless of whether you use passwords or certificates.
 | Protecting PDFs with file encryption software |
If you are looking to just send PDF files securely then file encryption software can be just as effective as PDF encryption software but can protect additional file types as well. The downside is that you and recipients need to use the same application (or one that supports the file format used for protected files).
It is best to avoid file encryption software that uses passwords since password cracking software may be available for those applications, although they usually target the most common file formats such as PDF and office documents.
 What is the best file encryption software to protect PDF files?
What is the best file encryption software to protect PDF files?
Perhaps the most successful file encryption software (and email content) has been Phil’s Pretty Good Privacy, or PGP. It will encrypt whole files regardless of the contents, can transport the decryption key in a safe and secure form, and deliver it to multiple recipients whilst allowing some certainty as to the identity party that encrypted the file.
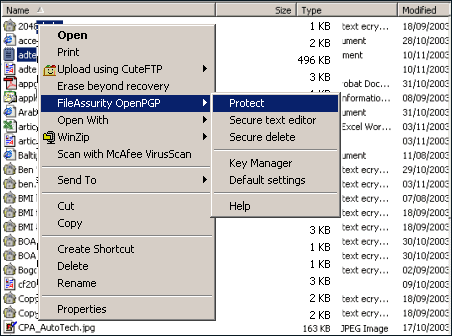
Encrypting a file with FileAssurity OpenPGP
File encryption software such as PGP (or any OpenPGP software) makes use of Public Key Infrastructure (PKI) to identify the creator of the encrypted file and the public identity of the recipient without allowing that information to be used to break into the system readily. They keep the content secret unless an authorized recipient opens them and they also provide alteration detection to check that the content has not changed since the owner encrypted it.
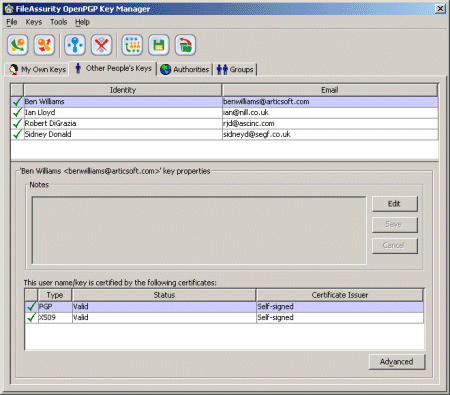
FileAssurity OpenPGP key management
PKI based file encryption systems are highly resistant to attack by anyone who does not have an appropriate key to decrypt the file. The biggest problem with file encryption systems is that they have no persisting controls for use of the file(s) they are protecting. So once the file has been decrypted the recipient can do anything they like with the file – unless there are DRM controls enforcing the use of a controlled environment for processing the protected PDF file.
 | Secure File Sharing Sites and one-time download links |
Another alternative to share PDF files securely is using secure file sharing sites. Many of these allow you to password protect the PDF and make it available for download for a number of days or via a one-time link (once the link has been clicked on to download the PDF it cannot be used again).
Filr for example is a WordPress plugin that enables you to upload and share files using secure download links on your web site. It enables you to restrict file access and limit the number of downloads available to users and automatically expire file download links on a specified date.
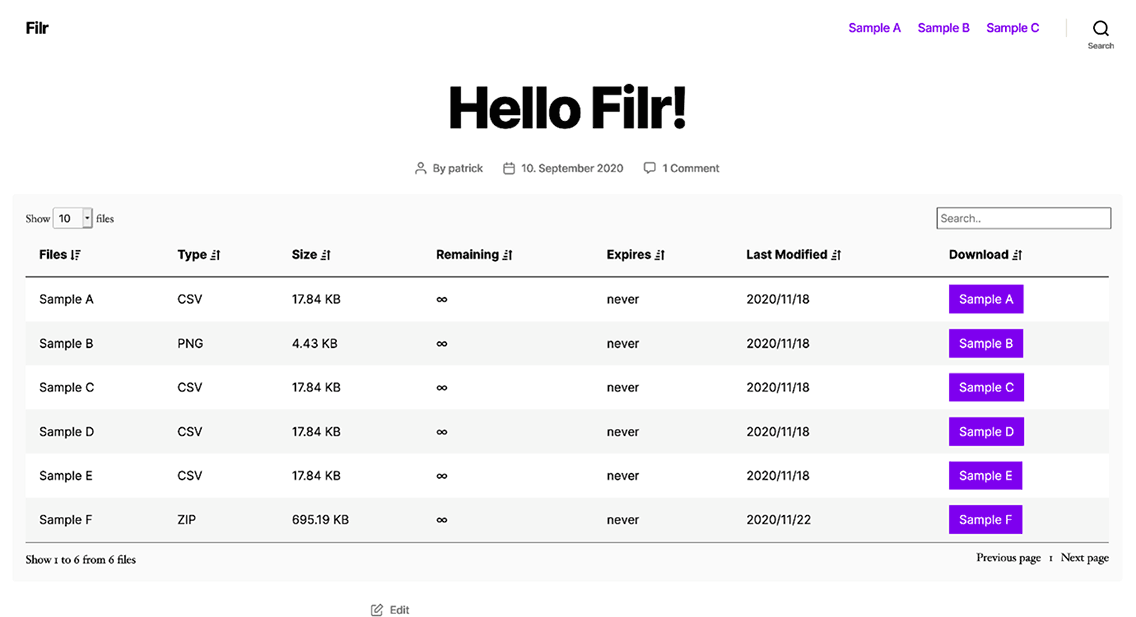
Creating secure download links in WordPress with Filr
 Do secure download links provide any real protection?
Do secure download links provide any real protection?
The problem is that once the user has downloaded the PDF file, they can then distribute it as they please. In other words, they do not offer any real protection against unauthorized distribution. They only prevent hackers from gaining access to your PDF files by requiring them to enter a password on the initial download to access it. Once a legitimate user has downloaded a file via the secure link they can then distribute it as they wish.
 | Protecting PDF documents in Secure Data Rooms |
Secure data rooms enable you to upload PDF files to a cloud server where they can be viewed by users in their browser. You can set limited controls to prevent copying of content (many convert PDF files to images so users cannot copy text in the browser), disable printing and add limited expiry controls.
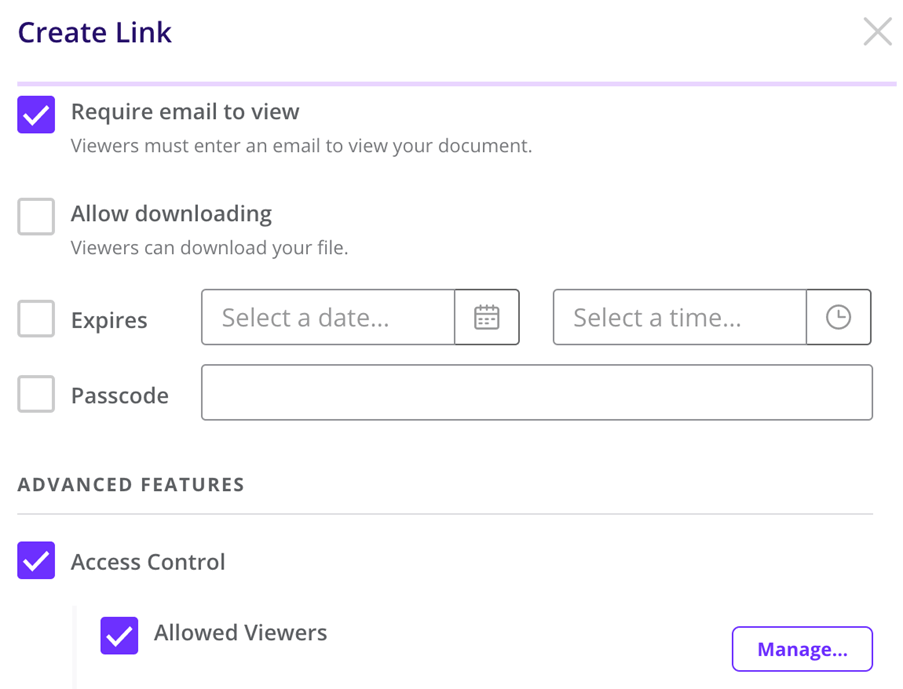
Creating a link to a document in DocSend
 Are secure data rooms safe?
Are secure data rooms safe?
Secure data rooms provide a low level of document protection. The main weakness of these systems is that:
- users must login to view PDF documents and they can share those login credentials with others including any 2FA information
- JavaScript is used to enforce security controls and this is susceptible to browser updates and plugins which could disable the protection
- browsers were not built for security so protection can be bypassed by users editing or removing the JavaScript in the browser’s debugger console
- if printing is allowed, users can print to unprotected PDF files
- users can take high quality screenshots with screen grabbing software that automatically screengrabs content as they view and scroll through it
- IP tracking is pretty useless since users regularly change IP address, and/or multiple users can use the same IP address by using shared proxies or VPNs
So while they appear to be a convenient and secure solution for protecting PDF files, the security can be easily bypassed.
 | Protecting PDF documents with Adobe Rights Management |
Adobe Experience Manager Forms is the rebadged version of Adobe LiveCycle ES2 which uses policy servers to control PDF use. Essentially you can protect PDF files with a certificate or a password and apply some restrictions such as preventing editing and printing, control expiry, and add watermarks. You can also audit PDF use.
However, the system is complex to setup as it relies on a series of policies and controls applied to PDF documents and other assets. You have to login to a server to add and apply policies and users connect to the server for those policies to be enforced.
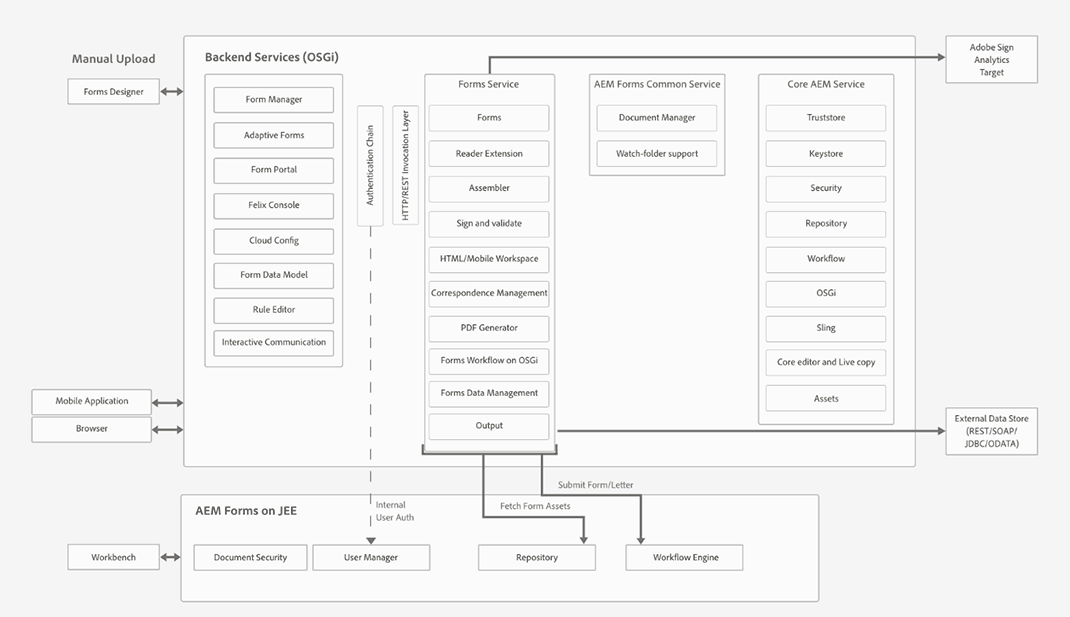
AEM Forms architecture and deployment topologies
Adobe Experience Manager document security would not be a good fit for example for a small business, as it is expensive and is primarily aimed at large enterprises who have LDAP, ADS and other such systems in place, and an IT team who can properly administer the system.
 | Protecting PDF files without passwords using PDF DRM |
A different approach to protecting PDF files is using a PDF DRM system that uses encryption and licensing controls. Locklizard for example use this approach to securely transfer document decryption keys to authorized user’s devices and then store them in an encrypted keystore that is locked to the device. This removes the need for both passwords and certificates – PDF files are transparently decrypted if the user has the correct key made available to them.

Protecting a PDF using Locklizard Safeguard PDF DRM software
PDF DRM systems also have the advantage over PDF restrictions in that controls cannot be easily removed as they are persistently enforced by the application. Some systems use JavaScript or plugins to Adobe Acrobat to achieve this, some use browser-based systems where users must login to view protected PDF files, and others use dedicated secure PDF Readers.
You should be aware that some PDF DRM software forces users to enable JavaScript in Adobe or disable security features. These types of systems should be avoided at all costs because they expose user’s systems to attack by hackers should they click on a malicious PDF file.
A dedicated PDF reader is a more secure approach since it has control over the environment – plugins only work within the application so you cannot prevent screen grabbing and other functionality that may be used to bypass the PDF protection, and users can easily share login credentials with others in browser-based systems and manipulate and bypass JavaScript protection.
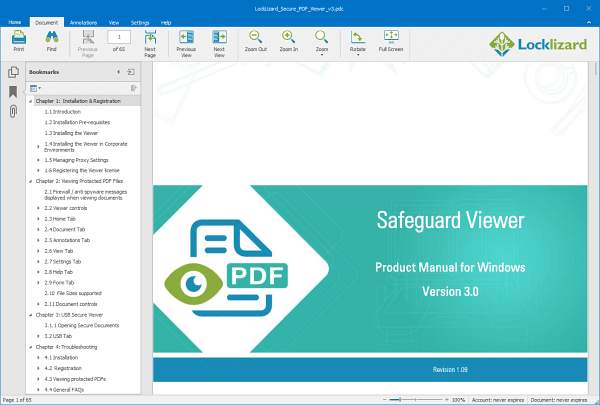
Safeguard Secure PDF Reader
Commonly PDF DRM systems will enable you to:
- Disable PDF printing
- Stop screenshots
- Expire PDF files
- Lock PDF files to devices and locations
- Restrict PDF use – copying, editing, saving to unprotected formats
- Add dynamic watermarks that cannot be removed
- Track PDF opens and prints
One of the most important security features of a PDF DRM system is locking PDF files to devices so they cannot be easily shared with others. Combined with transparent key delivery, this can provide the ultimate in PDF protection.
 | What is the best way to protect PDF files from copying, editing & printing? |

There are many ways you can protect PDF files, from using password and certificate encryption, digital signatures, licensing and DRM controls. The method you choose will depend on how confidential, sensitive or valuable your PDF documents are and whether you just want to securely send PDF files, protect them while they are being stored, share PDF files securely, sell them, or just control how they are used.
In summary:
- Password protection is pretty useless – you have to trust the recipient to not pass on the PDF file with the password
- PDF restrictions provide NO PROTECTION since they can be easily removed
- Certificate encryption provides better protection for sending PDF files securely since you don’t have to find a secure way to distribute keys
- File encryption software can protect many types of files, but just like PDF password and certificate encryption, give you no control over how they are used once decrypted
- Secure data rooms provide an easy way to share PDFs but they provided limited security and costs soon escalate
- Adobe Rights Management provides better protection than standard PDF password security but it is expensive and complex to setup and maintain
- PDF DRM software that uses JavaScript or plugins should be avoided since they require users to lower or turn off security on their devices
- PDF DRM solutions that use dedicated Viewers provide the best protection since they have control over the environment, can lock PDFs to devices to prevent sharing, and enforce watermarks and DRM controls which cannot be removed
What you need to bear in mind is if the protection can be easily bypassed or removed, or puts users’ systems at risk, then there is not much point applying it to begin with.









 Free Trial & Demo
Free Trial & Demo What do PDF restrictions do?
What do PDF restrictions do? Why can PDF restrictions be so easily removed?
Why can PDF restrictions be so easily removed? Are PDF passwords secure?
Are PDF passwords secure? Which encryption algorithm is strongest?
Which encryption algorithm is strongest? Additional issues with password encryption
Additional issues with password encryption What do Digital Signatures do?
What do Digital Signatures do? Is certificate encryption more secure than password encryption?
Is certificate encryption more secure than password encryption? What is the best file encryption software to protect PDF files?
What is the best file encryption software to protect PDF files? Do secure download links provide any real protection?
Do secure download links provide any real protection? Are secure data rooms safe?
Are secure data rooms safe?















