DRM Software: copy protection for PDF Documents, Files, Ebooks
Our PDF DRM software enforces DRM controls, uses US Government strength encryption (AES), real-time licensing, and public key technology. There are no passwords, Plugins, JavaScript, or zero footprint solutions to compromize your security, or complex PKI structures to manage. Why Safeguard’s better than secure data rooms.
We protect PDF files from copying, leakage, piracy, and sharing, ensuring your IP is always protected regardless of its location.

Safeguard PDF Security
Safeguard PDF Security prevents unauthorized access to PDF files, enables secure document sharing and distribution of PDF documents, controls what users can do with them, and how long they can be used.
More...

Enterprise PDF DRM
Enterprise rights management for large publishers and corporates who need all the features of Safeguard plus the ablity to track document use, restrict location access, make batch changes, run reports, and much more.
More...
DRM Software & Copy Protection Features

Stop copying, editing, saving
No complicated policy controls – disables functions used to modify or share content

Expiry & self-destruct
Automatically expire PDF access after a number of views, prints, days or on a fixed date

Stop or control printing
Stop printing or limit prints, enforce print quality and stop printing to PDF & other file formats

Stop Screenshots
Stop printscreen and third party screen grabbers (even remote ones) from taking screenshots

Dynamic Watermarks
Watermarks identify the user and deter content redistribution of photos and printouts

Location Locking
Control BYOD & where documents are used by locking use to specific locations (e.g. office only)

API Integration
Automate PDF protection & delivery – batch protect PDFs & integrate with shopping carts

Simple & Flexible Hosting
Host on premise or use our ready-to-go AWS hosted systems with flexible licensing options

Total Security
No insecure plugins, passwords, JavaScript, or uploading unprotected files to the web
| Safeguard PDF Security |
Enterprise PDF DRM |
Secure PDF Viewers | |
|---|---|---|---|
| Prevent unauthorized viewing | |||
| Prevent sharing | |||
| Prevent copying & modifying | |||
| Stop screen capture | |||
| Prevent printing or control no. of prints | |||
| Expiry (no. of views, days, fixed date) | |||
| Revocation of users & documents | |||
| Control online/offline use | |||
| Flexible online/offline use options | |||
| Dynamic watermarks | |||
| Log document views & prints | |||
| Restrict access to IP & country | |||
| License transfer across devices | |||
| Batch changes | |||
| Custom expiry & welcome messages | |||
| Backup & Restore | |||
| Generate Reports | |||
| Sub Administrators |
 Safeguard or Enterprise
Safeguard or Enterprise
Which PDF DRM system is right for me? – comparison chart.
DRM software add-ons
 |
Ecommerce/API integration |
 |
Command Line Encryption |
 |
Web Publisher |
 |
USB Security |
 |
Own Branding |
 |
Custom Registration Email |
 Award winning PDF DRM
Award winning PDF DRM
Our PDF DRM protection takes you beyond domain level security such as that used by Microsoft RMS, enabling companies to securely exchange documents in different environments without demanding that you or your customers implement a specific infrastructure. Document DRM Security Awards.
Digitial Rights Management Software Features
Our DRM software – document security and ebook DRM copy protection – stop your PDF files being shared by unauthorized users, and control how they are used by authorized users and for how long. They protect documents regardless of location, ensuring you have full control over use both inside and outside your organization.
Secure and transparent key management means there are no keys to enter, manage, or distribute. Protect PDF files without passwords or certificates, prevent data leakage, stop sharing and piracy. Digital Rights Management software that provides persistent protection both online and offline.
 Stop Document Sharing
Stop Document Sharing
Our DRM software uses encryption, DRM restrictions and licensing controls to stop unauthorized sharing of your documents.
We do not use passwords to protect documents since they can be easily shared with others or simply removed using freely available password removal software. Documents are protected using unique encryption keys that are securely and transparently relayed to authorized devices from a cloud server and stored encrypted in a keystore on the local device. The keystore is locked to individual devices and will not function if it is copied and moved elsewhere. So if users try to share your protected documents with others the recipients won’t be able to open them as they do not have access to the decryption keys.
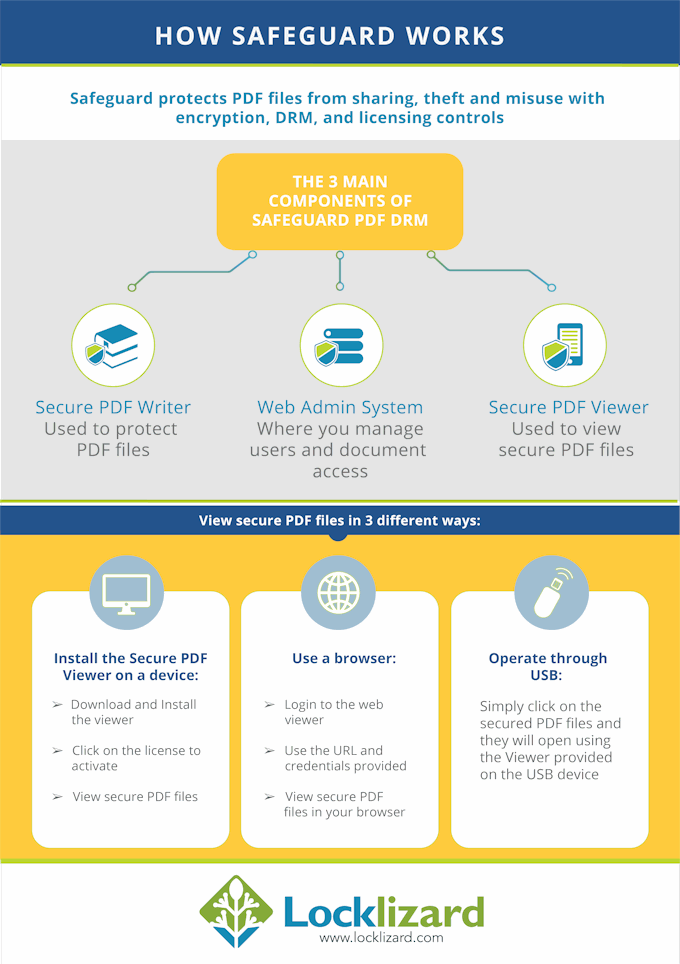
Protected documents can only be opened using our secure Viewer software which decrypts content in memory (using decryption keys from the keystore) and applies the appropriate DRM controls. Our secure Viewer software can either be installed on a device (Windows, Mac, iOS, Android), run from a USB stick (completely offline zero installation solution), or accessed via a web browser (zero installation).
 Stop Copying, Editing, Saving
Stop Copying, Editing, Saving
Our DRM software stops users from saving documents in unprotected formats – there is no ‘Save As’ option or ability to convert to other file formats using third party software – so only copies of protected files can be made. A copy of a protected file is of no use to another user without the decryption key to open it. And decryption keys are stored encrypted in a keystore which is locked to the device it was registered on – so only authorized users can open protected documents.
There is no option that can be enabled in our secure document Viewers for users to edit or copy/paste content – we disable copy & paste functionality and there is no editing facility available so text cannot be highlighted for selection and copied and pasted into other applications.
 Revoke Documents & Users
Revoke Documents & Users
As well as expiring access to PDF files automatically after a certain amount of time, or limiting the number of times a PDF can be opened, Safeguard enables you to manually revoke access to PDF files.
Being able to revoke documents is an important part of any document security solution. There may be times when the wrong document was published, a user has left your company, a payment has been revoked, or you think a specific document has been compromised.
Our DRM software enables you to revoke documents and/or users instantly. Documents can be revoked no matter where they reside.
 Lock documents to devices, domains, IPs
Lock documents to devices, domains, IPs
Our DRM software locks documents to authorized machines or devices so they cannot be used on other unauthorized devices.
You can also lock documents to specific countries, a domain or an IP address range in order to restrict use to a specific location (e.g. an office in the US) so that protected documents (stored for example on a laptop) will not open outside this location.
 Secure Document Hosting & Distribution
Secure Document Hosting & Distribution
Locklizard provides secure document hosting with Web Publisher (protected PDF files are stored on a cloud server either hosted by Locklizard or yourselves) or you can distribute protected documents as you would any other file.
Many providers offering secure document hosting protect your documents online so unprotected files are available on a server for a length of time before they are protected. Our secure cloud storage system (Web Publisher) protects documents locally (encryption and DRM controls applied) and then uploads them securely to a cloud server so they can never be compromised by server vulnerabilities.
If you prefer to host your protected documents then you distribute them like any other file (email, USB, web site download, etc.). Locklizard protected documents can only be opened by authorized users using our secure document Viewers. It does not matter who gets hold of your secure documents – unauthorized users won’t be able to open them – so you can make them freely available via a web site for download without worrying about password access controls.
For completely offline secure document distribution you can use Safeguard PDF Portable to distribute our secure Viewer and documents on USB sticks. Users can start using protected documents as soon as they receive their USB sticks without having to install any software. Additional protected documents can be added at a later date by authorized users when they become available without the USB stick having to be returned to you.
The administration system (where you create users and authorize document usage) can be hosted by Locklizard or on your own servers. This is separate from generating your secure documents (locally on your computer) so you have greater control over secure distribution of your documents and who has access to them.
We don’t lock you into monthly pricing like some document security providers – you can purchase annual and perpetual licenses.
 Document Expiry
Document Expiry
You can automatically expire documents so they can no longer be used after a certain amount of time:
- expire documents on a fixed date
- expire documents after a number of days
- expire documents after a number of opens or views
- expire documents after a number of prints
These options can also be used together – e.g. you can enter say a number of days/views/prints and a fixed date and whatever occurs first causes the document to expire.
Expiry dates can be changed on the administration system at any time and publishers can modify the number of views/prints available for each user.
 Stop Document Printing
Stop Document Printing
Our DRM software disables printing by default.
You can however enable unlimited printing, limit the number of times a PDF can be printed, or allow only degraded printing (black & white or grayscale).
You can make a PDF print disabled for all users when protecting it, and enable printing for individual users at a later date. Document watermarking is recommended if you allow printing to discourage photocopies of printed materials being made.
We disable print to PDF and other file printers so if you allow printing, users cannot print to PDF files, XPS, or any other unprotected file format.
 Stop Screenshots
Stop Screenshots
Our secure document viewers stop screenshots being taken by Windows print screen and common third party screen capture applications.
No DRM software however can stop all screenshots (and of course users can just take photographs of the screen) so it is recommended that document publishers apply dynamic watermarks as a copying deterrent. If a user’s name and email are displayed on a screen shot (by adding a dynamic watermark) they will probably be less likely to share it with others – this is especially true when uploading it to the Internet where they can be easily identified.
 Track & Log PDF use
Track & Log PDF use
With our Enterprise Rights Management solution you can log document use and see when users have viewed and/or printed your documents. This is useful if you want to track PDF files to check whether a particular user has viewed a document especially if they claim to have not received it.
You can see which are your top 5 most accessed, viewed and printed documents, who accessed them and when, and export this information to a CSV file.
 Non-removable & Dynamic Watermarks
Non-removable & Dynamic Watermarks
No DRM system is fool-proof. Even if screenshots are prevented, users can take photographs of the screen using a camera. Similarly, if printing is allowed, users can print and scan back in printed documents.
To discourage users making copies of protected documents, you can apply dynamic watermarks to viewed and/or printed documents. By using dynamic variables, you only have to protect a document once for all users (rather than watermarking and protecting each document individually for each user) as user data (name, company, email, date/time, etc.) is inserted at view/print time.
Unlike Adobe watermarks, our PDF watemarks are permanent and cannot be easily removed using PDF editing software.
 Remote File Deletion
Remote File Deletion
Some document security, DRM software, and Enterprise Rights Management solutions claim to be able to remotely delete files. However this is nothing more than a mere marketing ploy.
If a user has backed up the files before they were deleted then only the original file is deleted and not the backup. So the ‘deleted’ files will still exist. The important point is making sure a document is no longer usable and this can be achieved using expiry and revocation. If a secure document expires or is revoked it can no longer be used so any copy of the original is worthless to the user.
So while we do not provide remote file deletion in our DRM software, we do ensure access will cease when you decide.